2023-02-15 09:52:46 +00:00
|
|
|
|
**⭐PRs or any form of contribution will be appreciated⭐**
|
2023-02-15 09:25:28 +00:00
|
|
|
|
|
2022-02-24 11:56:02 +00:00
|
|
|
|
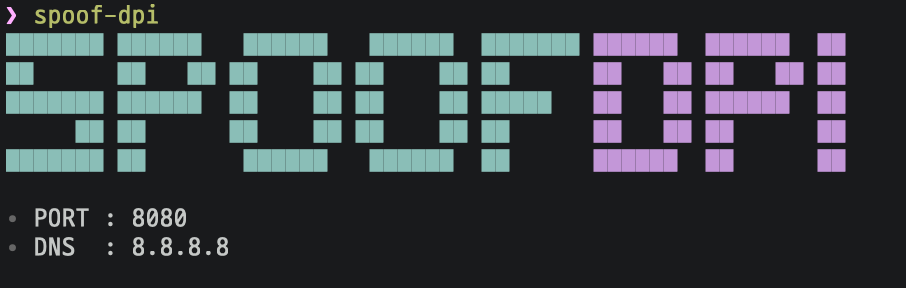
# SpoofDPI
|
|
|
|
|
|
|
2024-08-14 23:54:46 +00:00
|
|
|
|
选择语言: [🇬🇧English](https://github.com/xvzc/SpoofDPI), [🇰🇷한국어](https://github.com/xvzc/SpoofDPI/blob/main/_docs/README_ko.md), [🇨🇳简体中文](https://github.com/xvzc/SpoofDPI/blob/main/_docs/README_zh-cn.md), [🇷🇺Русский](https://github.com/xvzc/SpoofDPI/blob/main/_docs/README_ru.md), [🇯🇵日本語](https://github.com/xvzc/SpoofDPI/blob/main/_docs/README_ja.md)
|
2024-08-06 22:47:32 +00:00
|
|
|
|
|
|
|
|
|
|
|
2022-02-24 11:56:02 +00:00
|
|
|
|
|
|
|
|
|
|
规避**深度包检测**的简单工具
|
2024-08-04 19:02:56 +00:00
|
|
|
|
|
2022-02-24 11:56:02 +00:00
|
|
|
|
|
|
|
|
|
|
|
2024-08-26 11:54:54 +00:00
|
|
|
|
# Installation
|
|
|
|
|
|
See the installation guide for SpoofDPI [here](https://github.com/xvzc/SpoofDPI/blob/main/_docs/INSTALL.md).
|
2022-02-24 11:56:02 +00:00
|
|
|
|
|
|
|
|
|
|
# 使用方法
|
|
|
|
|
|
|
|
|
|
|
|
```
|
|
|
|
|
|
Usage: spoof-dpi [options...]
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-addr string
|
2024-07-27 02:00:53 +00:00
|
|
|
|
listen address (default "127.0.0.1")
|
2024-08-25 09:09:58 +00:00
|
|
|
|
-banner
|
|
|
|
|
|
enable banner (default true)
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-debug
|
2024-07-27 02:00:53 +00:00
|
|
|
|
enable debug output
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-dns-addr string
|
2024-07-27 02:00:53 +00:00
|
|
|
|
dns address (default "8.8.8.8")
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-dns-port int
|
2024-07-27 02:00:53 +00:00
|
|
|
|
port number for dns (default 53)
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-enable-doh
|
2024-08-06 08:48:10 +00:00
|
|
|
|
enable 'dns-over-https'
|
|
|
|
|
|
-pattern value
|
|
|
|
|
|
bypass DPI only on packets matching this regex pattern; can be given multiple times
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-port int
|
|
|
|
|
|
port (default 8080)
|
2024-08-05 08:07:53 +00:00
|
|
|
|
-system-proxy
|
|
|
|
|
|
enable system-wide proxy (default true)
|
2024-07-21 08:21:56 +00:00
|
|
|
|
-timeout int
|
2024-08-06 08:48:10 +00:00
|
|
|
|
timeout in milliseconds; no timeout when not given
|
|
|
|
|
|
-v print spoof-dpi's version; this may contain some other relevant information
|
2024-07-27 02:00:53 +00:00
|
|
|
|
-window-size int
|
|
|
|
|
|
chunk size, in number of bytes, for fragmented client hello,
|
|
|
|
|
|
try lower values if the default value doesn't bypass the DPI;
|
2024-08-03 06:58:17 +00:00
|
|
|
|
when not given, the client hello packet will be sent in two parts:
|
|
|
|
|
|
fragmentation for the first data packet and the rest
|
2022-02-24 11:56:02 +00:00
|
|
|
|
```
|
|
|
|
|
|
|
|
|
|
|
|
> 如果你在 Chrome 浏览器使用其他 VPN 扩展比如 Hotspot Shield 请去 设置 > 扩展程序禁用它们
|
|
|
|
|
|
|
|
|
|
|
|
### OSX
|
2024-08-06 08:48:10 +00:00
|
|
|
|
运行 `spoof-dpi` ,然后它会自动设置自身为代理
|
2022-02-24 11:56:02 +00:00
|
|
|
|
|
|
|
|
|
|
### Linux
|
2024-08-06 08:48:10 +00:00
|
|
|
|
运行 `spoof-dpi` 然后加上代理参数运行你的浏览器
|
|
|
|
|
|
```bash
|
|
|
|
|
|
google-chrome --proxy-server="http://127.0.0.1:8080"
|
|
|
|
|
|
```
|
2022-02-24 11:56:02 +00:00
|
|
|
|
|
|
|
|
|
|
# 工作原理
|
|
|
|
|
|
|
|
|
|
|
|
### HTTP
|
|
|
|
|
|
|
|
|
|
|
|
因为世界上许多网站都已支持 HTTPS ,SpoofDPI 不会规避对 HTTP 请求的 DPI,但是它仍会为 HTTP 请求提供代理。
|
|
|
|
|
|
|
|
|
|
|
|
### HTTPS
|
2024-08-07 04:30:32 +00:00
|
|
|
|
尽管 TLS 加密了握手的每一步,但是在 Client Hello 中的域名仍然是明文的。因此如果有人看到 Client Hello 包就可以知道你在连接什么网站。这给 DPI 提供了很大方便,我们也看到连接在 Client Hello 之后就会被屏蔽掉。我之前尝试了规避这种审查,并发现,如果把 Client Hello 分包,只有第一个 chunk 会被检测。SpoofDPI 只要在第一个分包发送 1 byte,然后再发送其他部分就能规避。
|
2024-08-04 19:02:56 +00:00
|
|
|
|
|
2022-02-24 11:56:02 +00:00
|
|
|
|
# 启发
|
|
|
|
|
|
|
2024-08-26 11:54:54 +00:00
|
|
|
|
[Green Tunnel](https://github.com/SadeghHayeri/GreenTunnel) by @SadeghHayeri
|
2022-02-24 11:56:02 +00:00
|
|
|
|
[GoodbyeDPI](https://github.com/ValdikSS/GoodbyeDPI) by @ValdikSS
|